Limit Login Attempts: The WordPress Plugin To Save You From Brute Force Attack
Posted On : February 10th, 2015 By : Durga Prasad Kundu To : WordPress, WordPress PluginsBrute Force Attack: The Most Common Way of Hacking
Brute force attack is one of the most favorite ways of hacking by hackers worldwide. It simply refers to hacking the login details through automated software. With this hackers can have a combination of seemingly infinite numbers of ids and passwords and by trying these they can easily log into our website. After login they have all the control over every data we have in the server.
Choosing Username & Password; Be Careful!!!
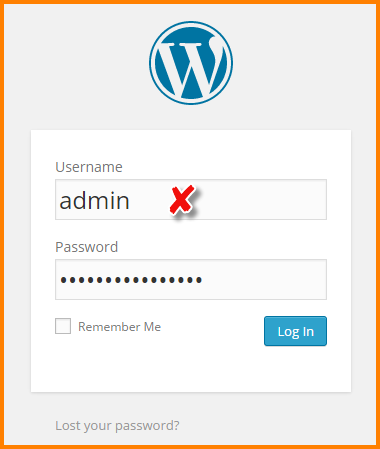
Most WordPress site owners prefer “admin” as username and safely presume no problem in it as this is default choice in WordPress. So, around 90% of brute force attacks try to crack the username “admin”.If the site owner has opted a
different username unlike admin then it will be difficult for the hackers to crack both the id and password. The reason is hackers have to match numbers of ids and passwords combination rather than matching only passwords with a known username i.e. admin.
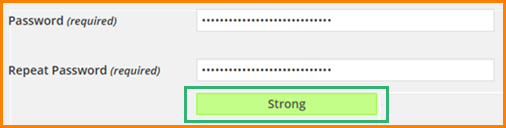
Also never opt for generic passwords like qwerty, admin, 123456, admin123 and some of those generic passwords are now running in your mind; you can take them as reference to avoid. It is found that in most cases of Brute force attack, site owners have such easy-to-guess passwords for log in. Be smart & choose a password with all combinations supported so that it will be difficult to guess. Come on; it’ll take hardly some seconds to decide one such strong password! Also have a look on the WordPress Password Strength indicator while creating a password. The stronger it is, the more difficult will be to break it.
But the fact is how much strong it is, there is every chance that it might be hacked now or then. So, you are thinking about a permanent solution! Well, Limit Login Attempts is a beautiful and worthy WordPress plugin to save your site from such brute force attack.
What is Limit Login Attempts Plugin
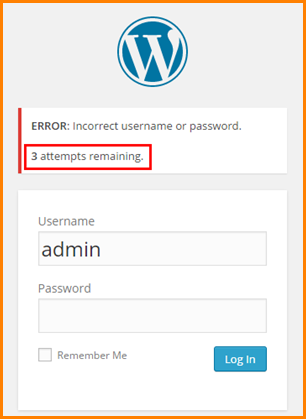
The basic requirement is; as it is a WordPress plugin so it is obvious that it is meant for sites designed in WordPress only. Like different useful plugins of WordPress, this Limit Login Attempts plugin is a useful one and allow us to restrict hackers to get into the admin data or to the dashboard by limiting the number of login attempts. Definitely no one wants others to access one’s dashboard and manipulate the whole thing.
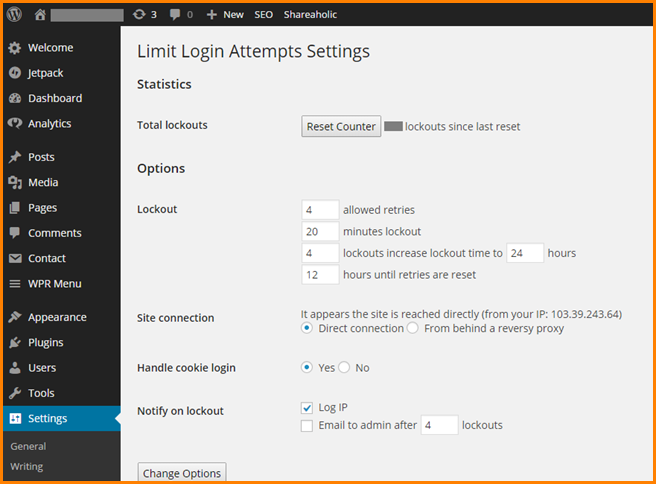
Steps to install Limit Login Attempts & setting options
- Log in to your site
- Go to “Plugins” section
- Search for “Limit Login Attempts” & install it
- Set different options as per your requirement
- Set how many retries to be allowed
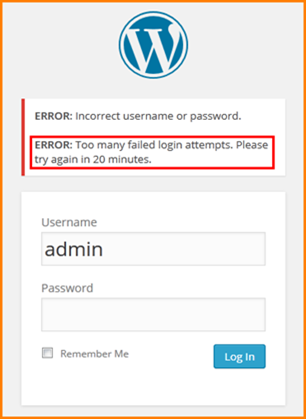
- Set after how much time one can try again after the first failed attempt
- Set whether cookie login to be allowed or not
- Set whether the login IP needs to be reported or not
Is it not very simple to install, definitely yes? You don’t have to be a technical wizard to do it! Now you shouldn’t be worried about brute force attack anymore. Would you? Otherwise your web design team will do it for you.
Yes, I know that you are going to ask what would happen when the real admin gets blocked somehow due to failed attempts. Not a big deal! You may wait for the time set for retry. Or if you have other IPS, you may login with that and can deactivate the plugin so that you can again login with the normal IP. And after that you may reactivate the plugin again. Even you may reset the counter or the number of lockouts to ZERO.
Keep in mind that our site must have direct connection that means our site must not reach behind a reverse proxy.
Avoiding Brute Force Attack through Coding
Also, through coding we can restrict other users’ login attempts. What we can do? Hmm…., you can set your own proxy for login purpose and those trying to login to the site with a different proxy will be denied. Yeah, it is a great idea but, how we can achieve it.
Here goes the code:
AuthUserFile /xxx/null
AuthGroupFile /xxx/null
AuthName "WordPress Admin Access Control"
AuthType Basic
order deny,allow
deny from all
# whitelist admin's IP address
allow from xx.xx.xx.xxx
# whitelist admin1's IP address
allow from xx.xx.xx.xxx
# whitelist admin2's IP address
allow from xx.xx.xx.xxx
# whitelist admin3's IP address
allow from xx.xx.xx.xxx
# whitelist Work IP address
allow from xx.xx.xx.xxx
But wait; where to write that code? In the .htaccess file. Heartbeat increased? Any web design guy knows the risk associated with this particular file present in the root directory. With a minor mistake in this file, your site may be vanished into air. It may not be accessed at all.
But here I’m talking about the .htaccess file present in the wp-admin folder. The above mentioned code should be placed in there. I repeat; it should be placed in the .htaccess file present in the wp-admin file not in the file in root directory. If there is no such file in wp-admin folder then there is a chance that the .htaccess file is hidden, so check for that first and if not available then create one .htaccess file; write the code there and upload the file to the wp-admin folder.
And now no one can access your dashboard with proxy IPs other than specified IP.
Conclusion:
I know there are hundreds of ways to hack a site. But hacking through brute force attack or accessing the admin with multiple try by automated software is very common now and can be done by anyone without in-depth knowledge. Even anyone knows you may guess and login to the admin after 5 to 10 retry. But by installing such a beautiful plugin “Limit Login Attempts”, you can be sure about the safety of your site from such type of hacking. Now, it is the time to apply it and get out of the problem.
So, “Happy Coding”!
- How Content-Visibility CSS Property Can Boost Rendering Performance? - August 7, 2020
- Key Takeaways From SEMrush Conference on YouTube SEO - December 18, 2019
- This Is Why You Shouldn’t Use a White PNG Logo - February 13, 2018




Hey buddy you have done a good job. After all website security means a lot. Thanks for this post and update.